We take a holistic view of IT security and focus on the solution, not the products. This enables our customers to implement IT security projects much faster and often realise time and cost savings.
German companies are legally obliged to fulfil regulatory requirements for company-wide IT security and to invest in the implementation of measures. These can vary depending on the country, industry and type of data processed.
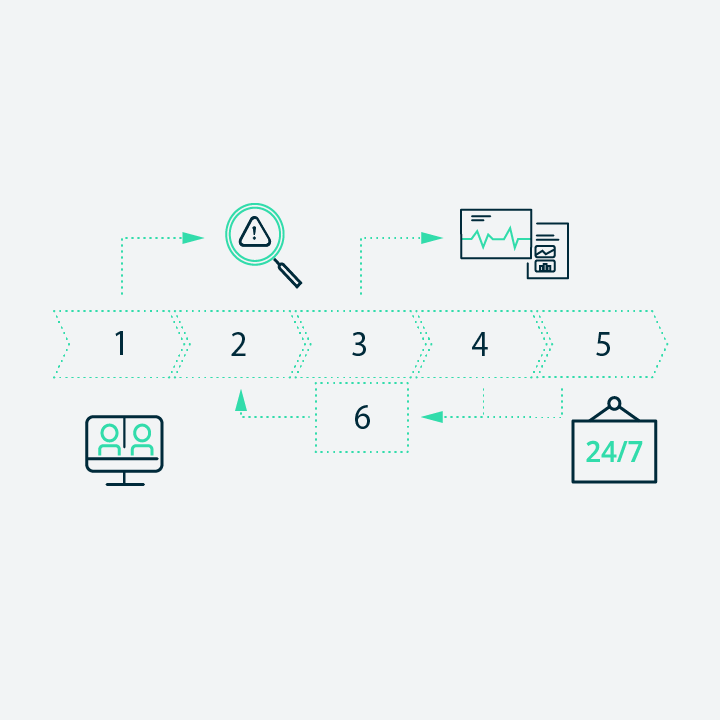
With our holistic approach, we build a bridge from security consulting to technology suppliers. We develop strategies and customised solutions and also support you with implementation in your organisation as well as efficient operation and future controls. Customised and flexible, tailored to your needs. From the data centre to the perimeter to the cloud, this saves time and internal resources.